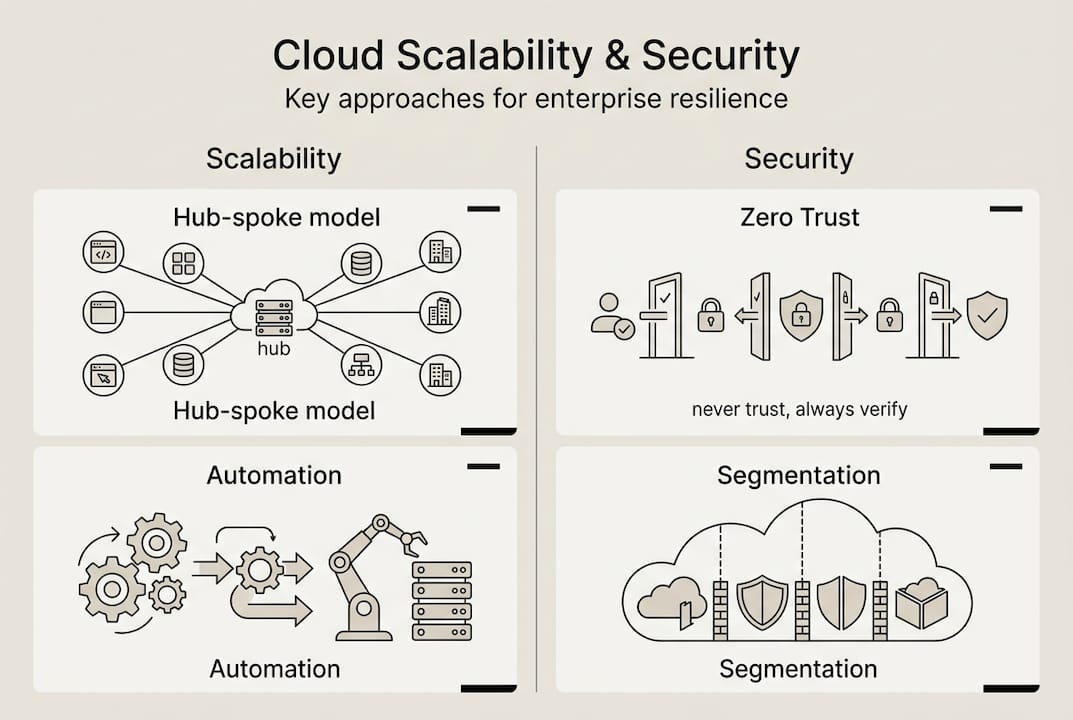
Most IT managers assume cloud scalability hinges on compute power and storage capacity. Yet connectivity is a core component of cloud infrastructure, enabling data transmission between on-premises, VPCs, and multi-cloud environments through hub-and-spoke models. Without robust connectivity architecture, even the most powerful cloud resources become bottlenecks. This guide reveals how connectivity shapes cloud performance, explains architectural models that scale efficiently, and delivers practical strategies for IT managers and system administrators optimizing hybrid, multi-cloud, and edge deployments for both security and growth.
Table of Contents
- Key takeaways
- Understanding cloud connectivity fundamentals
- Challenges and risks in cloud connectivity management
- Optimizing connectivity for SMBs and enterprises
- Future-proofing your cloud connectivity strategy
- Explore advanced cloud connectivity solutions with Internetport
- FAQ
Key Takeaways
| Point | Details |
|---|---|
| Hub and spoke scalability | Modern cloud connectivity relies on a central hub that routes between multiple spokes to dramatically reduce point to point connections and keep network growth linear. |
| Control plane separation | Distinguishing control plane from data plane ensures traffic can continue flowing when routing decisions or configuration updates momentarily fail, improving reliability. |
| Connectivity approaches | VPN, Direct Connect, Internet exchange, and software defined networking overlays cover secure remote access private links and programmable connectivity options. |
| SMBs vs enterprises needs | Small and midsize businesses favor cost and simplicity while enterprises require governance security and scalable controls to manage complex deployments. |
Understanding cloud connectivity fundamentals
Cloud connectivity serves as the data transmission backbone linking on-premises infrastructure, virtual private clouds, and multi-cloud environments. This networking layer determines how efficiently workloads communicate, how securely data traverses networks, and how seamlessly organizations scale distributed systems. Without proper connectivity architecture, cloud resources remain isolated islands incapable of delivering integrated business value.
Modern cloud connectivity relies heavily on hub-and-spoke architectural models. AWS Transit Gateway and Google Cloud's Network Connectivity Center exemplify this approach, where a central hub manages routing between multiple spoke networks. This design dramatically reduces the number of point-to-point connections required as environments grow. Instead of managing connections that scale exponentially with each new VPC or site, organizations maintain linear growth in network complexity. The hub becomes a single control point for traffic inspection, policy enforcement, and routing optimization.
Understanding the distinction between control plane and data plane proves essential for reliable cloud operations. The control plane handles routing decisions, configuration updates, and network state management. The data plane forwards actual traffic based on those decisions. When these planes operate independently with proper separation, data can continue flowing even if control plane updates temporarily fail. This architectural principle underlies many resilience strategies discussed later.
Cloud connectivity encompasses several technical approaches:
- VPN connections establish encrypted tunnels over public internet for secure remote access and site-to-site linking
- Direct Connect or dedicated circuits provide private, high-bandwidth links bypassing public networks entirely
- Internet exchange connectivity enables peering with multiple networks at colocation facilities for optimized routing
- Software-defined networking overlays abstract physical topology for programmable, flexible connectivity management
SMBs typically start with VPN-based connectivity for cost efficiency and ease of deployment. Enterprises often combine multiple approaches, using Direct Connect for production workloads requiring predictable latency while maintaining VPN backup paths. The choice depends on bandwidth requirements, security posture, budget constraints, and geographic distribution of resources.
Challenges and risks in cloud connectivity management
Managing cloud connectivity introduces complexities that directly impact both scalability and security. Control plane failures can cascade globally despite healthy data planes, causing major outages like the 2025 AWS US-EAST-1 DNS issue. During that incident, DNS resolution failures in the control plane prevented new connections and service discoveries even though existing data flows continued unaffected. The blast radius extended globally because applications worldwide depended on centralized control plane services for routing decisions.
Control plane disruptions differ fundamentally from data plane problems. A data plane failure stops traffic forwarding immediately and visibly. Control plane issues create subtler problems: routing tables stop updating, new connections fail to establish, and configuration changes hang indefinitely. Systems may appear functional until cached state expires, then fail catastrophically. This delayed failure pattern makes control plane health monitoring critical yet often overlooked.
"The 2025 outages revealed how tightly coupled control planes create systemic risk. Organizations that assumed regional isolation would protect them discovered their applications depended on global control plane services they didn't fully understand."
Operational challenges compound as cloud footprints expand:
- Multi-cloud sprawl creates inconsistent networking policies across providers, increasing misconfiguration risk
- Hybrid connectivity between on-premises and cloud introduces latency variability affecting real-time applications
- Edge computing pushes workloads closer to users but multiplies the number of network endpoints requiring management
- Governance becomes complex when teams provision cloud resources independently without centralized network oversight
Security risks emerge from improper network segmentation and insufficient Zero Trust implementation. Traditional perimeter-based security assumes internal networks are trustworthy, but cloud environments blur these boundaries. Without micro-segmentation and continuous authentication, lateral movement after initial compromise becomes trivial. Many breaches exploit overly permissive security groups and network ACLs that grant broader access than necessary.

Pro Tip: Monitor control plane state distance metrics and implement Route53 (or equivalent) health checks to preempt disruptions. Track how long control plane updates take to propagate and set alerts when propagation delays exceed baselines. This early warning system helps you detect control plane degradation before it causes visible failures. For more insights on managing infrastructure resilience, explore the cloud outage technical analysis resources available.
Optimizing connectivity for SMBs and enterprises
Organizational scale fundamentally shapes cloud connectivity priorities. SMBs prioritize cost efficiency and ease of integration, while enterprises focus on governance, security, and managing multi-cloud complexity. These different priorities demand tailored approaches to connectivity architecture and tooling.
For SMBs, connectivity optimization starts with these practical steps:
- Begin with SaaS-integrated solutions that bundle connectivity with applications, reducing the need for specialized networking expertise
- Implement cost monitoring tools to track data transfer charges, which often surprise organizations new to cloud economics
- Use hybrid cloud strategically, keeping latency-sensitive workloads on-premises or in nearby edge locations while leveraging cloud for burst capacity
- Start with managed VPN services from cloud providers before investing in dedicated circuits, scaling connectivity investments as traffic grows
- Leverage cloud provider native tools like AWS VPC peering or Azure Virtual Network peering before adopting third-party networking solutions
Enterprises require more sophisticated approaches given their scale and compliance requirements. Infrastructure as Code becomes essential for managing IP address allocation across hundreds of VPCs. Tools like Terraform or CloudFormation ensure consistent network configuration and enable rapid disaster recovery. Zero Trust architectures over encrypted tunnels replace legacy VPN concentrators, authenticating every connection request regardless of network location. Governance frameworks establish approval workflows for network changes, preventing shadow IT from creating security gaps.
| Consideration | SMB Approach | Enterprise Approach |
|---|---|---|
| Cost management | Pay-as-you-go, minimize fixed costs | Reserved capacity, negotiate volume discounts |
| Control | Leverage managed services | Build custom networking with granular policies |
| Complexity | Simplicity over features | Comprehensive tooling for complex environments |
| Security | Cloud provider defaults plus basic hardening | Zero Trust, micro-segmentation, compliance frameworks |
| Scalability | Scale reactively as needs grow | Architect for future scale proactively |
Pro Tip: Use hub-and-spoke models like AWS Transit Gateway to simplify multi-VPC communication and scalability. Instead of managing full-mesh connectivity between VPCs, route everything through a central transit hub. This reduces the number of connections from N*(N-1)/2 in a full mesh to just N connections in hub-and-spoke, dramatically simplifying operations as your environment grows.
Hybrid and edge-cloud approaches offer compelling benefits for latency-sensitive applications. Real-time video processing, IoT data aggregation, and interactive gaming all benefit from edge computing that reduces round-trip times to end users. Virtual private servers deployed at edge locations can preprocess data before sending aggregated results to centralized cloud analytics platforms, balancing operational costs against performance requirements. This tiered architecture keeps hot data close to users while archiving cold data in cost-effective cloud storage.
Future-proofing your cloud connectivity strategy
Long-term cloud connectivity resilience demands architectural patterns that minimize failure blast radius. Edge cases like 2025 outages highlight the need for cell-based isolation and benchmarking provider performance before embracing multi-cloud and hybrid models. Cell-based architecture partitions infrastructure into independent failure domains, ensuring problems in one cell don't cascade to others. Each cell maintains its own control plane instance, preventing the global control plane failures that plagued 2025.
Benchmarking provider performance becomes critical as organizations adopt multi-cloud strategies. Throughput, latency, jitter, and packet loss vary significantly between providers and regions. Testing these metrics under realistic load conditions before committing workloads prevents costly migrations later. Edge locations particularly require validation since performance can degrade rapidly with distance from provider backbone networks.
| Provider/Model | Avg Throughput | Latency (p95) | Security Features | Scalability |
|---|---|---|---|---|
| AWS Transit Gateway | 50 Gbps per VPC | <1ms intra-region | VPC isolation, route filtering | Thousands of VPCs |
| Azure Virtual WAN | 20 Gbps per hub | 2-5ms regional | Firewall integration, encryption | Hub-spoke to 2000 VNets |
| Google Cloud Interconnect | 100 Gbps dedicated | <2ms to GCP | Private connectivity, MACsec | Scales with circuit count |
| SD-WAN overlay | Varies by underlay | 5-50ms internet-based | Encrypted tunnels, segmentation | Limited by controller |
Continuous monitoring and fault tolerance require investment in observability platforms that track both control and data plane health. Key metrics include:
- Control plane API response times and error rates indicating degradation before complete failure
- Data plane packet loss, latency distributions, and throughput trends revealing capacity constraints
- Route propagation delays showing how quickly network changes take effect across your environment
- Connection establishment success rates catching authentication or routing problems
Static stability principles allow data planes to operate on cached state when control planes become unavailable. This approach requires designing systems that gracefully degrade rather than fail completely when they can't reach control services. Health checks should validate data plane functionality independently from control plane status, enabling traffic to flow even during control plane maintenance or failures.
Automation and continuous integration practices keep pace with cloud complexity. Network configuration should be version-controlled, tested in staging environments, and deployed through CI/CD pipelines just like application code. This discipline prevents configuration drift and enables rapid rollback when changes cause problems. Hybrid and edge networking solutions benefit particularly from automation since managing distributed infrastructure manually becomes impractical at scale.
Disaster recovery provisioning ensures you can rebuild connectivity quickly after catastrophic failures. Document network topologies, maintain configuration backups in multiple regions, and regularly test recovery procedures. Many organizations discover their disaster recovery plans are incomplete only during actual incidents when missing details prevent rapid restoration.
Explore advanced cloud connectivity solutions with Internetport
Optimizing cloud connectivity requires infrastructure partners who understand both technical complexity and business priorities. Internetport delivers flexible cloud solutions tailored to SMBs and enterprises seeking robust connectivity and scalable infrastructure. Whether you're building hybrid architectures, managing multi-cloud environments, or deploying edge computing, the right foundation matters.
Explore webhosting services for application hosting with integrated connectivity, VPS hosting solutions for customizable virtual infrastructure, or colocation server offerings for deploying your hardware in carrier-neutral facilities with direct cloud on-ramps. These options support hybrid and multi-cloud strategies while maintaining the security, reliability, and performance your operations demand. Internetport's infrastructure helps you implement the connectivity best practices covered in this guide with technical support that understands your challenges.
FAQ
What is the role of connectivity in cloud architecture?
Connectivity enables communication between cloud components, on-premises data centers, and multi-cloud environments, forming the foundation for scalability and security. Efficient connectivity models like hub-and-spoke reduce complexity and improve performance by centralizing routing decisions and minimizing the number of network connections required as infrastructure grows.
How do control plane failures impact cloud connectivity?
Control plane failures disrupt routing and configuration management, often causing widespread outages even when data forwarding remains unaffected. These failures prevent new connections from establishing and stop configuration updates from propagating. Static stability approaches allow data planes to operate on cached state, reducing downtime risk by enabling traffic flow during control plane disruptions.
What connectivity strategies best suit SMBs versus enterprises?
SMBs typically prioritize cost efficiency, simplicity, and SaaS integration, starting with managed VPN services and scaling connectivity investments as traffic grows. Enterprises focus on governance, security controls, multi-cloud management, and scalable architectures, implementing Zero Trust frameworks and Infrastructure as Code to manage complex networking requirements across distributed environments.
How can I improve the resilience of my cloud connectivity?
Implement redundant control plane resources and use data-plane failover mechanisms like health checks to maintain service during component failures. Adopt monitoring for both control and data plane state, tracking metrics like API response times and packet loss. Embrace hybrid cloud architectures to reduce latency and increase reliability by keeping critical workloads closer to users while leveraging cloud for scalability.
