TL;DR:
- Most exploits succeed despite hosting providers' defenses, highlighting the need for active security measures.
- Hosting security encompasses comprehensive practices like patch management, access controls, and layered defenses.
- Regular audits, proper configuration, and a shared security responsibility are essential to reduce risks.
Most IT managers assume their hosting provider handles security. That assumption is expensive. A 2026 Patchstack study that tested 11 real-world vulnerabilities across major hosting platforms found an average block rate of just 25.89%, meaning roughly 74% of exploits succeeded despite provider defenses. For privilege escalation attacks specifically, only 12% were stopped. These are not edge cases or exotic zero-days. They are the kind of vulnerabilities your applications face every week. This article gives you a practical, data-backed breakdown of what hosting security actually covers, where the gaps are, and what your team needs to do about it.
Table of Contents
- What is hosting security and why does it matter?
- Core components: Tools, practices, and benchmarks
- Security across hosting types: Shared, VPS, dedicated, and cloud
- Mitigating real-world vulnerabilities: From WAF to layered defense
- The uncomfortable truth about hosting security: Why most organizations are still at risk
- Secure your hosting the right way with Internetport
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Hosting security essentials | True hosting security involves layered defenses, not just provider promises or default setups. |
| Shared responsibility | Both provider and client have key roles in maintaining a secure hosting environment. |
| Defense-in-depth works | A multi-layered strategy combining WAF, OS hardening, and regular updates best blocks attacks. |
| Continuous vigilance needed | Regular audits and testing are necessary since most breaches result from overlooked basics and misconfigurations. |
What is hosting security and why does it matter?
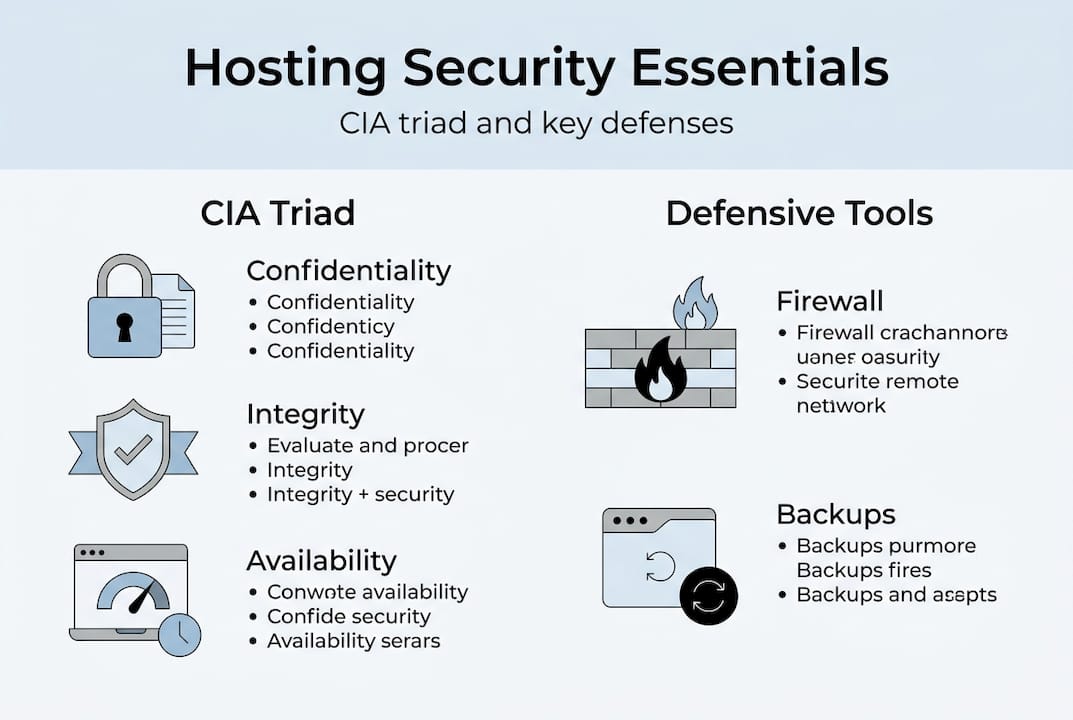
The phrase "secure hosting" appears on nearly every provider's homepage. But marketing language and operational reality rarely match. Hosting security is not a checkbox or a single product feature. It is, as described in the Hosting Security Hardening Checklist, the comprehensive set of practices, configurations, and tools applied to web hosting environments to protect servers, applications, and data from unauthorized access, attacks, and breaches, ensuring the CIA triad.
The CIA triad, which stands for confidentiality, integrity, and availability, is the foundation of every serious security program. Confidentiality means only authorized users can access your data. Integrity means your data has not been tampered with. Availability means your systems stay online when your business needs them. A hosting environment that fails any one of these three pillars creates real operational and financial risk.
For SMBs, a single breach can mean days of downtime, loss of customer trust, and regulatory exposure. For enterprises, the stakes scale up fast: multi-system compromise, data exfiltration, and potential PCI DSS or GDPR violations. Yet most organizations focus only on the network perimeter, ignoring the server-level configurations and application-layer gaps that attackers actively exploit.
Here is what hosting security actually covers beyond the marketing brochure:
- Server and OS hardening: disabling unused services, patching kernels, restricting SSH access
- Access controls: enforcing least privilege, multi-factor authentication, and role separation
- Network defenses: firewalls, intrusion detection systems, and DDoS mitigation
- Application protections: web application firewalls (WAFs), input validation, and dependency updates
- Data protection: encrypted storage, automated backups, and secure transfer protocols
- Monitoring and response: real-time alerting, log analysis, and incident response planning
"Most breaches do not come from sophisticated nation-state actors. They come from unpatched software, weak credentials, and misconfigured servers that have been sitting exposed for months."
Before building your security stack, a solid web hosting checklist helps ensure you are asking the right questions. And if you are still evaluating which environment fits your organization, hosting types explained gives a grounded comparison to inform your decision.
Core components: Tools, practices, and benchmarks
Understanding what hosting security covers is step one. Knowing which components actually move the needle is where most teams fall short. A hardened hosting environment is built from several layers, each addressing a distinct attack surface.
A well-secured host implements a combination of server hardening, security headers, WAFs, firewalls, 2FA/MFA, automatic backups, malware scanning, and kernel tuning against DDoS. Each of these plays a specific role and none of them works in isolation.
Here is a priority-ordered list of what your team should verify or configure:
- Patch management: Apply OS and application patches within 24 to 72 hours of release. Unpatched systems are the single most exploited entry point.
- SSH hardening: Disable password authentication, use key-based login, and restrict SSH to known IP ranges.
- Security headers: Configure HTTP response headers to prevent clickjacking, cross-site scripting, and content sniffing.
- WAF deployment: Use a WAF to filter known malicious patterns before they reach your application.
- File permissions: Set strict permissions on web root directories. World-writable files are an open invitation.
- Automated backups: Daily off-site backups with tested restore procedures are non-negotiable.
- Log monitoring: Centralized logging with anomaly detection catches lateral movement early.
The data on security headers should concern you. A 2026 study of 10,000 websites found that HSTS adoption sits at only 51.7%, Content Security Policy at just 27.3%, and the average Mozilla Observatory score was 58 out of 100. Perhaps most alarming: 82.9% of sites leak server version information, handing attackers a free roadmap to known exploits.
| Security header | Adoption rate (2026) |
|---|---|
| HSTS | 51.7% |
| Content Security Policy | 27.3% |
| X-Frame-Options | ~60% |
| Server info exposure | 82.9% of sites |
| Avg Mozilla score | 58/100 |
Pro Tip: Run your production domain through Mozilla Observatory (observatory.mozilla.org) today. A score below 50 means you have fixable, high-priority gaps that take less than a day to address. Pair that with the hosting reliability for IT framework to prioritize which changes have the greatest business impact.
Security across hosting types: Shared, VPS, dedicated, and cloud
Not every hosting environment carries the same risk or puts the same responsibility on your team. Understanding this distinction is critical before signing any contract or allocating security budget.

Shared hosting relies on provider-level isolation, typically via CloudLinux, while VPS requires manual hardening. The "secure hosting" label providers apply to shared environments is technically accurate at the infrastructure level, but it says nothing about your application, your configuration, or your update practices.
| Hosting type | Provider responsibility | Your responsibility | Isolation level |
|---|---|---|---|
| Shared | OS patches, network security | App updates, config, credentials | Low (shared kernel) |
| VPS | Physical hardware, network | OS hardening, app security, firewall | Medium (virtualized) |
| Dedicated | Physical hardware only | Everything from OS up | High (bare metal) |
| Cloud | Infrastructure, base images | Config, app security, IAM | Variable |
Key considerations when evaluating your current setup:
- Shared hosting is appropriate for low-risk static sites or early-stage projects. It should not host any application processing sensitive customer data.
- VPS hosting gives you root access and full control, but that control is only valuable if your team uses it. An unhardened VPS is more dangerous than shared hosting because you own the failure.
- Dedicated servers offer the strongest isolation and performance, making them the right choice for regulated industries or high-traffic environments.
- Cloud hosting introduces IAM complexity. Misconfigured access policies are one of the top causes of cloud breaches.
If you are managing workloads that require strong isolation without the overhead of a full dedicated build, VPS hosting advantages explains where VPS delivers genuine security value. For organizations ready to evaluate environment fit at scale, enterprise hosting selection walks through a structured process. Internetport's LXC VPS platform provides container-level isolation that significantly limits blast radius if one instance is compromised.
Mitigating real-world vulnerabilities: From WAF to layered defense
Knowing your hosting type and configuring the right tools is essential. But how well do those tools perform against actual attack scenarios? The answer is sobering.
74% of tested exploits succeeded despite active hosting defenses. WAFs and infrastructure controls catch generic, signature-based attacks reliably. What they miss are application-layer exploits, logic vulnerabilities, and attacks targeting specific plugin or framework behavior. A WAF does not know your application's business logic. It cannot detect when a legitimate-looking request abuses a broken access control flaw.
A layered defense strategy combines server hardening, WAF, vulnerability mitigation, and regular updates into a system that compensates for each layer's blind spots. No single control is sufficient. Think of it as defense in depth: if one layer fails, the next one catches what slipped through.
Here is what a practical layered defense looks like for most organizations:
- Layer 1 (Infrastructure): Hardened OS, patched kernel, restricted SSH, network firewall
- Layer 2 (Network): WAF filtering inbound traffic, rate limiting, DDoS mitigation
- Layer 3 (Application): Dependency updates, secure coding practices, input validation, output encoding
- Layer 4 (Detection): Real-time log monitoring, anomaly alerts, file integrity monitoring
- Layer 5 (Response): Incident response playbook, tested backup restoration, communication plan
74% of exploit attempts bypass default hosting defenses. That number should drive every security budget conversation your team has in 2026.
Pro Tip: Schedule a quarterly penetration test focused specifically on your application layer, not just infrastructure. Provider-level scans miss the logic flaws that real attackers find manually. Pair this with managed webhosting solutions that include proactive monitoring to reduce your detection-to-response window.
The uncomfortable truth about hosting security: Why most organizations are still at risk
Here is something most hosting vendors will not tell you: their security tools are designed to protect their infrastructure, not your application. Imunify360, Sucuri, and similar platform tools do a reasonable job blocking known malware and generic attack signatures. But app-layer vulnerabilities remain invisible to infrastructure security because those tools have no context for your application's logic.
We have seen this pattern consistently: organizations invest in a "secure" managed hosting plan, assume coverage is complete, and skip internal security reviews for years. Then a logic flaw in a plugin or a misconfigured role permission opens a door that no provider tool was ever built to close.
The IT managers who actually stay ahead of this are not the ones with the biggest security budgets. They are the ones who treat hosting security as a shared responsibility and verify it regularly. They run their own audits. They test restore procedures. They review access logs. They do not trust provider dashboards as their primary signal.
If your team wants a structured baseline, hosting security strategies gives a practical framework for enterprise-grade environments. The gap between promise and reality closes only through active, ongoing effort, not one-time configuration.
Secure your hosting the right way with Internetport
If this article has made one thing clear, it is that real hosting security requires more than a marketing label. It requires infrastructure built with security as a design principle, not an afterthought.
At Internetport, our dedicated server solutions, webhosting services, and VPS hosting are built around proactive monitoring, daily automated backups, free SSL certificates, PCI DSS certified data centers, and platform configurations that align with the layered defense model this article describes. Whether you are running a growing SMB or managing multi-environment enterprise infrastructure, our team works with you to match the right solution to your actual risk profile. Reach out to discuss a setup that fits your security requirements.
Frequently asked questions
What is the CIA triad in hosting security?
The CIA triad stands for confidentiality, integrity, and availability, the three core pillars that every hosting security program must protect to maintain business continuity and data trust.
Which types of hosting are most secure?
Dedicated and properly hardened VPS hosting offer the strongest isolation, but "secure hosting" labels on shared environments cover only infrastructure, not your application layer.
Do providers' security tools like Imunify360 replace the need for updates and audits?
No. These tools address infrastructure-level threats, but a layered approach combining server hardening, WAF, active patching, and regular audits is the only way to cover application-layer risks.
How common are misconfigurations as a cause of hosting security breaches?
Over 70% of hosting breaches trace back to misconfigurations or unpatched systems, making regular configuration audits one of the highest-return security investments your team can make.
Recommended
- Enterprise hosting guide: Secure, scalable solutions
- Web hosting explained: Types, mechanics, and best solutions
- How reliable hosting empowers IT management for SMBs
- Cloud infrastructure explained: Scalable hosting for SMBs
- Complete Guide to Insurance Platform Security Fundamentals - Digital Insurance Platform | IBSuite Insurance Software | Modern Insurance System